Data Loss Prevention (DLP)

5 Tips for Managing Third-Party Risk
Across industries and around the world, executives remain preoccupied with digital transformation. According...
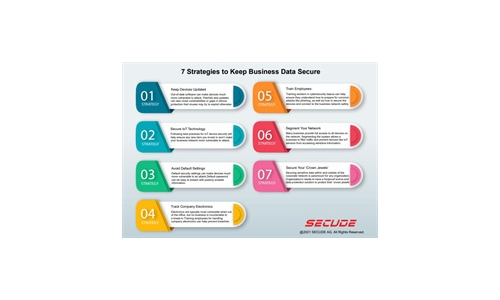
7 Strategies to Keep Business Data Secure
Read our simple infographic which headlines seven strategies to keep your business data secure. ...
Cloud Data Security 2023 Report by ESG, a division of TechTarget
…More than half (59%) of respondents believe that more than 30% of their organization's sensitive data...
The Definitive Email Cybersecurity Strategy Guide
Email is your most essential business tool—and today's top malware delivery vector. This vital communications...

The 10 Tenets of an Effective SASE Solution
As cloud adoption grows, cloud-enabled organizations are experiencing an influx of new security requirements....
Sign up for Cyber Security Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.