Encryption Key Management
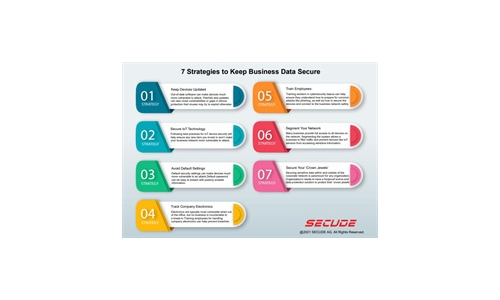
7 Strategies to Keep Business Data Secure
Read our simple infographic which headlines seven strategies to keep your business data secure. ...
UK National Cyber Strategy: BAE Systems Response
The new UK National Cyber Strategy represents a key moment in cyber policy and ambitions. Here, we reflect...
5 Reasons Why Software Security is More Critical Than Ever
Vulnerable software and applications are the leading cause of security breaches. Couple this with the...

Protecting your content against cyber threats and data loss
How the Content Cloud safeguards your most valuable information Your business runs on content — but...
The edge advantage
Reduce costs and improve performance with edge computing. Read The edge advantage, and you'll understand...
Supporting Success in Federal Government Healthcare
Automation, technology expertise, and a dedicated partnering philosophy are key to driving success. And...

First steps to data provisioning maturity
An organization's deepest insights are often derived from sensitive data. Responsible organizations know...

Hope is NOT a strategy: Secure your business with the Content Cloud
Seems like every week there's news of another security breach. Ponemon Institute has found that the typical...
Sign up for Cyber Security Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.

