Latest Whitepapers

The Definitive Guide to Data Security Posture Management (DPSM)
DSPM charts a modern path for understanding everything that affects the security posture of your data....

Hope is NOT a strategy: Secure your business with the Content Cloud
Seems like every week there's news of another security breach. Ponemon Institute has found that the typical...
Drive Real Behaviour Change
Cybersecurity awareness training is one of the most important things you can do to secure your organisation....
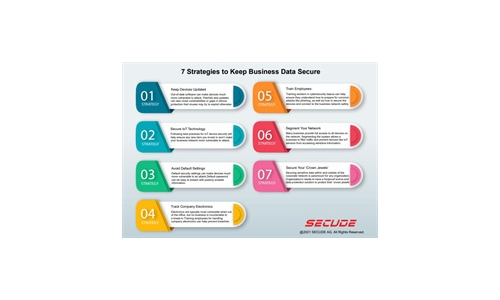
7 Strategies to Keep Business Data Secure
Read our simple infographic which headlines seven strategies to keep your business data secure. ...
AI Driven Threat Defense The Next Frontier in Cybersecurity
It's undeniable that the landscape of modern cybersecurity has evolved dramatically—and at a rapid...

7 Metrics to Measure the Effectiveness of Your Security Operations
You can't improve what you don't measure. To mature your security operations center (SOC) and security...
Phish in a Barrel: Real-World Cyber Attack Examples
What your users don't know about cyber threats can hurt them—and your organisation. They're constantly...
Cloud Cyber Resilience Report
After a dynamic year for cloud native apps, Tenable has compiled a report focusing on trends and recommendations...

Realizing The Devops Vision In Embedded Systems
Markets demand ever more complex systems and faster development cycles. Meanwhile, there is a shortage...

Raising the Bar for Web App and API Security
Most Web Application and API Security Isn't Enough Securing the web applications and APIs that underpin...
5 Tips for Modernizing a Security Operations Center
When an organization decides to modernize a Security Operations Center (SOC) or implement a more formal...

MSP Security Best Practices: Ransomware Attack Prevention
In Datto's Global State of the Channel Ransomware Report, 4 in 5 managed service providers (MSPs) agreed...
Sign up for Cyber Security Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.









