Data Security

Open Channels, Hidden Threats
How Communication and Social Media Tools Are Changing the Insider Risk Equation for Compliance, IT and...

CyberArk 2022 Identity Security Threat Landscape Report
A global report from CyberArk which shows that 79% of senior security professionals say that cybersecurity...
Redefining Data Loss Prevention (DLP)
Data doesn't move itself. People—whether they are negligent, compromised or malicious—move data in...
CIO Essential Guidance: CISO Security Threat landscape
After a year that saw the largest and fastest transformation in work patterns in history, security teams...
5 Reasons Why Software Security is More Critical Than Ever
Vulnerable software and applications are the leading cause of security breaches. Couple this with the...
A Visual Landscape Of Cybersecurity
Our world has never moved faster in terms of cyber threats, security technology innovations and overall...
The Top 10 Biggest and Boldest Insider Threats
Over the last two years alone, insider security incidents have jumped 47%, with the average cost per...
The Definitive Email Cybersecurity Strategy Guide
Email is your most essential business tool—and today's top malware delivery vector. This vital communications...

Pain & Progress: Cybersecurity and Business Risk Study
Despite their best efforts and investments, some organisations still experience difficulty as a result...
Security Control Guide: Hardened Services Guide
System Hardening is the process of securing a system's configuration and settings to reduce IT vulnerability...
2022 Cost of Insider Threats: Global Report
Independently conducted by Ponemon Institute External attackers aren't the only threats modern organisations...

5 Tips for Managing Third-Party Risk
Across industries and around the world, executives remain preoccupied with digital transformation. According...
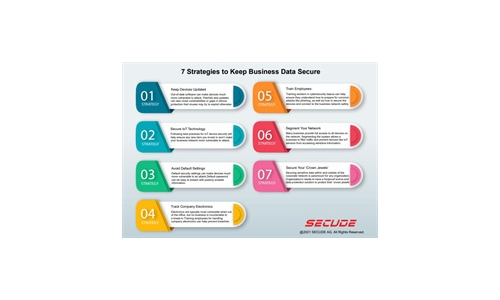
7 Strategies to Keep Business Data Secure
Read our simple infographic which headlines seven strategies to keep your business data secure. ...
Sign up for Cyber Security Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.