Data Security

The Definitive Guide to Data Security Posture Management (DPSM)
DSPM charts a modern path for understanding everything that affects the security posture of your data....
The Three Keys to Secure and Successful Cloud Migrations
To make cloud transformations as efficient and successful as possible, companies must remain secure and...
Zero Trust Privilege for dummies
Cyber breaches are bigger and worse than ever. Hardly a day goes by without headlines about some new...
Cloud Data Security 2023 Report by ESG, a division of TechTarget
…More than half (59%) of respondents believe that more than 30% of their organization's sensitive data...
Privileged Access Management Buyers' Guide
Security breaches show no signs of slowing, and credential theft headlines are the number one attack...
The Definitive Email Cybersecurity Strategy Guide
Email is your most essential business tool—and today's top malware delivery vector. This vital communications...
Network Security Approaches and the Case for Zero Trust
Top executives say that legacy network technical baggage is holding them back from transforming their...

The 4 Benefits of VPN Elimination
The corporate perimeter as you know it no longer exists. Virtual private network (VPN) vulnerabilities...

The CIO’s Guide to SASE Planning
Driving the future of work through enterprise-wide SASE The convergence of networking and network security...
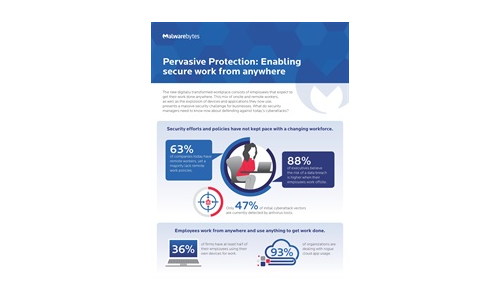
Pervasive Protection: Enabling Secure Work From Anywhere
The new digitally transformed workplace consists of employees that expect to get their work done anywhere....

PCI Compliance Best Practices
The Payment Card Industry Data Security Standard (PCI DSS) has been in place since 2004, with the latest...

Pain & Progress: Cybersecurity and Business Risk Study
Despite their best efforts and investments, some organisations still experience difficulty as a result...
CMMC Compliance Guide
On January 1, 2020, the United States Department of Defense (DoD) released its Cybersecurity Maturity...
Sign up for Cyber Security Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.