Network Security
Bridging the Gap of Grief with Business-Driven Security
Worldwide spending on information security products and services will reach $86.4 billion in 2017, an...
What Makes Real Threat Intelligence
First popularized in terminology several years ago, threat intelligence means many things to many people....
Modern Blueprint to Insider Threat Management
Taking a People-Centric Approach to Your Insider Threat Management (ITM) Programme Insider threats can...
Collective Defense: A radar-like view of cyber threats
IronNet is committed to answering the World Economic Forum's call to action for collaborative cyber defense....
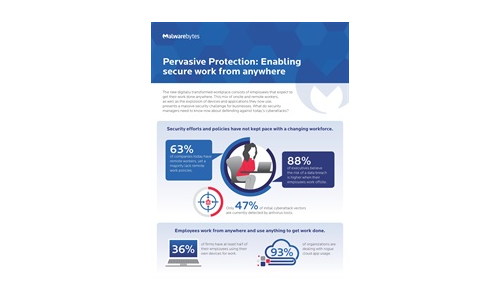
Pervasive Protection: Enabling Secure Work From Anywhere
The new digitally transformed workplace consists of employees that expect to get their work done anywhere....

Raising the Bar for Web App and API Security
Most Web Application and API Security Isn't Enough Securing the web applications and APIs that underpin...
Back to the Basics: Cyber Hygiene Starts with Asset Management
The challenge: managing millions of dynamic, distributed and diverse assets while maintaining high standards...

2021 Technology Industry Cyber Threat Landscape Report
The technology industry is a top target for both cybercriminals and state-sponsored cyber espionage groups....
Lay the Foundation for Zero Trust
Zero Trust has been a topic of discussion in the Federal Government for some time. However, the approach...

The Evolution of Cybersecurity
Cybersecurity Through the Years As we look at the ever-increasing, technology-dependent cyber environment...
When Networks Meet The New Tomorrow
This paper looks at IT priorities that organizations will need to address now and in the new tomorrow:...

5 Benefits of Partnering with Webroot
While cyberattacks continue to evolve in volume, organization, and sophistication, security technology...
Sign up for Cyber Security Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.



