System Security
The Definitive Email Cybersecurity Strategy Guide
Email is your most essential business tool—and today's top malware delivery vector. This vital communications...
NAIKON: Traces from a Military Cyber-Espionage Operation
NAIKON is a threat actor that has been active for more than a decade. The group focuses on high profile...
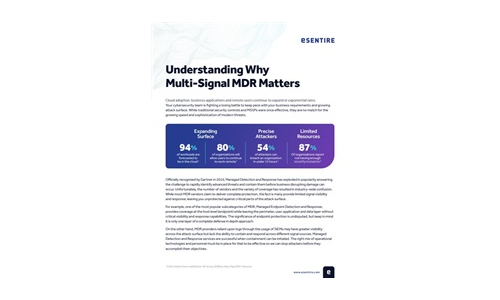
Understanding Why Multi-Signal MDR Matters
MDR providers can only detect and respond to what they can see. A multi-signal approach is paramount...
Protect K-12 Schools from Cyberattacks with Active Breach Protection
Ransomware is not just another buzzword. It is a very real threat to educational institutions of all...
Marketing Fraud Benchmarking Report
Marketing fraud comes in numerous flavors, some of which are eminently relatable to any internet user...

Cloud and Web Security Challenges in 2022
Organisations' work environments have undergone rapid but lasting changes in the face of the recent health...

Six Signs Your Email Gateway Might Need Replacing
Many organisations are spending way too much money on licensing the their email SPAM and malware gateway...

How Secure is your Cloud data
With employees working remotely at higher rates, business data is increasingly at risk. IT administrators...
Sign up for Cyber Security Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.