System Security

Cyber Attack Trends: Check Point’s 2022 Mid-Year Report
The war in Ukraine has dominated the headlines in the first half of 2022 and we can only hope that it...
5 Reasons Why Software Security is More Critical Than Ever
Vulnerable software and applications are the leading cause of security breaches. Couple this with the...
Secure Email Gateway: Buyer’s Guide
Protecting your organization against email-borne threats is only becoming more difficult as attackers...
The 7 Hidden Truths of Cloud Security
Based on extensive, up-to-date knowledge and experience from WithSecure consultants, threat hunters and...

Introducing a Cyber Security Service For Home WiFi
The renewal cycle for home WiFi routers is lengthy and involves users upgrading to a newer model once...

2021 Data Risk Report - Manufacturing
Our 2021 Manufacturing Data Risk Report focuses on the growing cybersecurity threats facing industrial...
CIO Essential Guidance: CISO Security Threat landscape
After a year that saw the largest and fastest transformation in work patterns in history, security teams...
Marketing Fraud Benchmarking Report
Marketing fraud comes in numerous flavors, some of which are eminently relatable to any internet user...
6 Signs Your Email Gateway Might Need Replacing
Our experts have looked at the 6 signs your email gateway might need replacing. Read our guide and squeeze...
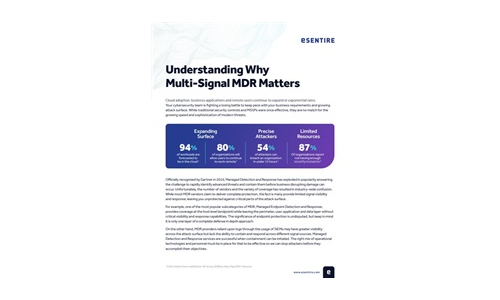
Understanding Why Multi-Signal MDR Matters
MDR providers can only detect and respond to what they can see. A multi-signal approach is paramount...
What is Zero Trust? (Really)
Over the last decade, cybersecurity has been focused on the challenge of securing increasingly vulnerable...
Sign up for Cyber Security Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.